
High-risk users are the top quartile of users in an organization who have had at least one instance of risky behavior, or event. These risky users are responsible for:
- 41% of all simulated phishing clicks
- 30% of all real-world phishing clicks
- 54% of all secure-browsing incidents
- 42% of all malware events
So where do high-risk users hide in organizations? The answer to this question seems to be “everywhere.” However, it’s a little more nuanced than that.
This latest Cyentia Institute Report, in partnership with Elevate Security, analyzed nearly eight years’ worth of data—from June 2014 to July 2022, and dives into:
-
What makes workers high risk
-
What are their riskiest behaviors
-
Where those high-risk users spend their time
-
What that might mean for your organization’s security
Download your copy of the report. ➡️
Learn More About Elevate Security
Elevate Security is redefining the cybersecurity landscape. Our SaaS platform integrates with leading security technologies to identify users most likely to cause a security breach and automatically orchestrate additional security measures to minimize the likelihood of a future incident.
Trusted by the World's Leading Companies



"Availability of User Risk Score from Elevate Security has been a game changer for us. Giving our people a more intuitive understanding of potential risks is a great addition to our security culture at a time of rapidly changing cybersecurity threats.”
— Daryl Harding, CISO, GHD
How Proactive Security Works
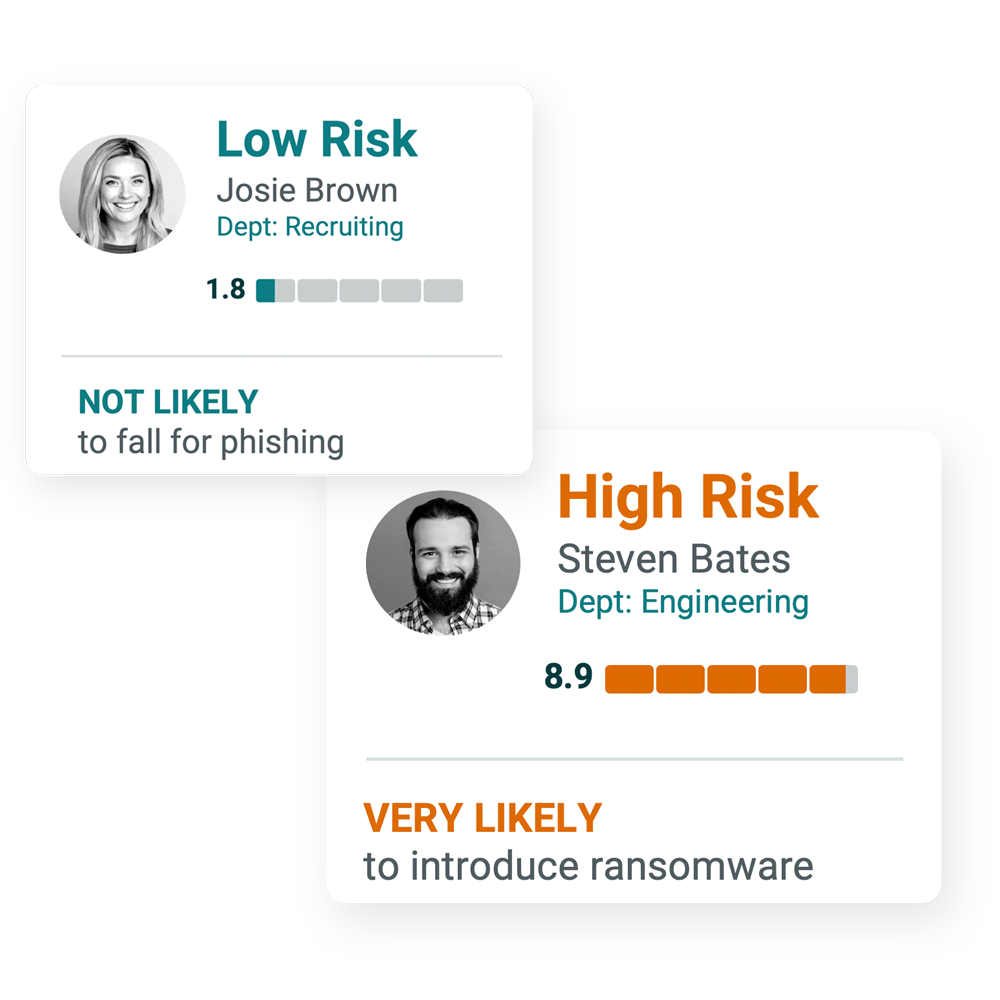
1. IDENTIFY the highest risk users
2. PROTECT with targeted controls
3. DRIVE reduced incidents
Why The Elevate Security Platform Is Unique
DEPTH
Access security controls, decision support, and dashboards with deep insights
BREADTH
Leverage security data and insights from your existing tools—with results in minutes
VISIBILITY
Quickly identify which users and contractors are most likely to cause a breach
CONTROL
Use risk scores, context, and automated policy changes to eliminate workforce risk
The Elevate Security Platform makes it easy to analyze and defend your organization against unintentional insider risk. Use benchmark visibility, targeted security controls, and personalized feedback to focus on risky employees & strengthen your cyber defenses.
Proactively address your insider risk and:

Mine insights from diverse user data

Predict the source of your next incident

Automate response to reduce risk


Monitor & measure your insider risk over time
Target controls for specific risks & risky employees
Personalize feedback based on individual employee risk
Stop Reacting. Start Preventing.
Get in front of incidents.
All of the information you need to understand and identify your riskiest users already exists in your enterprise. The Elevate Security Platform integrates and ingests this valuable employee security data from all your current cybersecurity tools and systems.